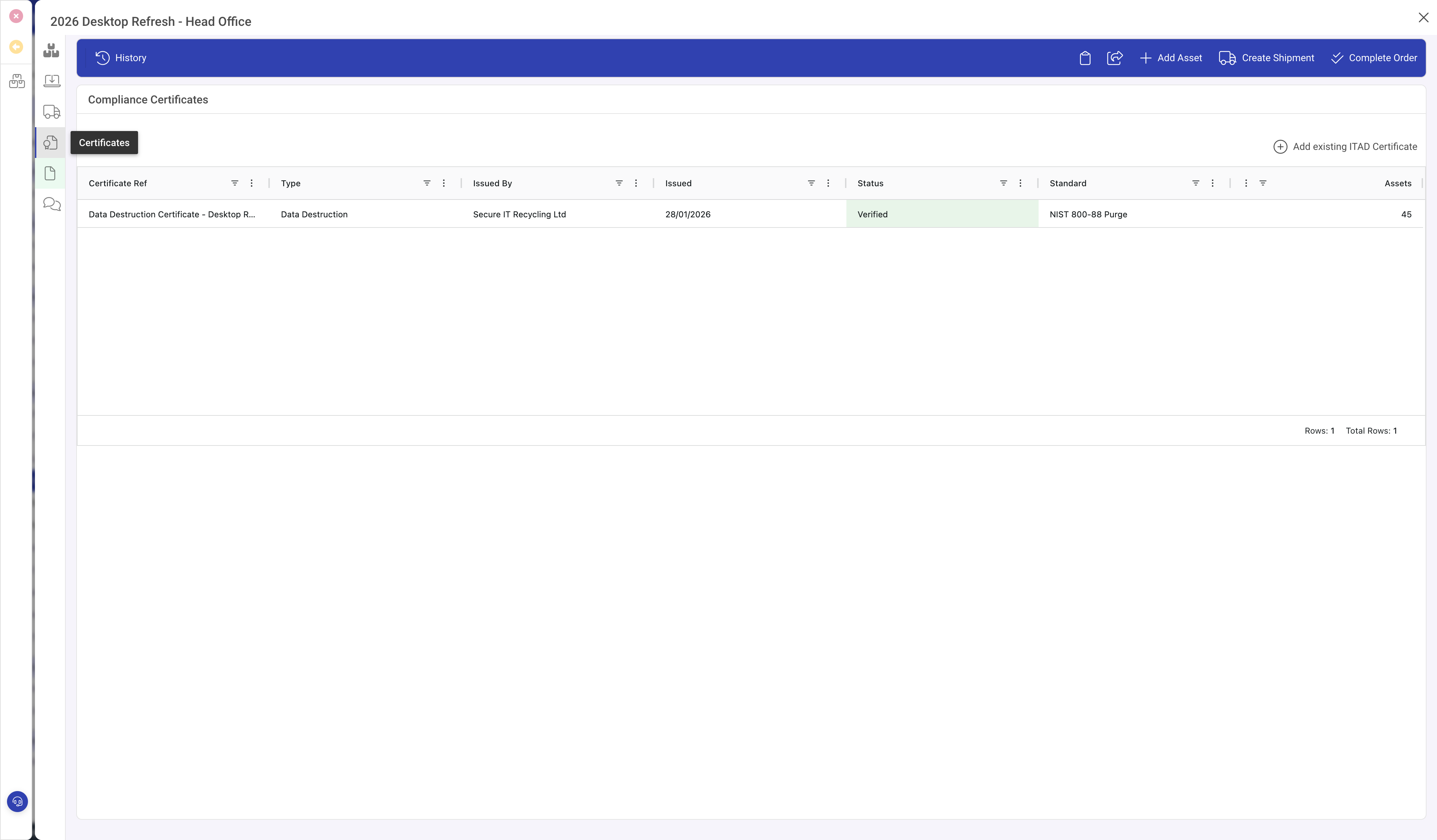
Disposition certificates provide formal compliance evidence for the ITAD process. They are issued by your ITAD vendor and verified internally.
Certificate types
- Data Destruction: confirms data sanitisation per NIST 800-88 or equivalent standard.
- Recycling: confirms WEEE-compliant processing and environmentally responsible disposal.
- WEEE Compliance: specific to EU/UK Waste Electrical and Electronic Equipment regulations.
- Duty of Care: waste transfer documentation required by environmental regulations.
- Waste Transfer: standard waste handling documentation.
Certificate detail
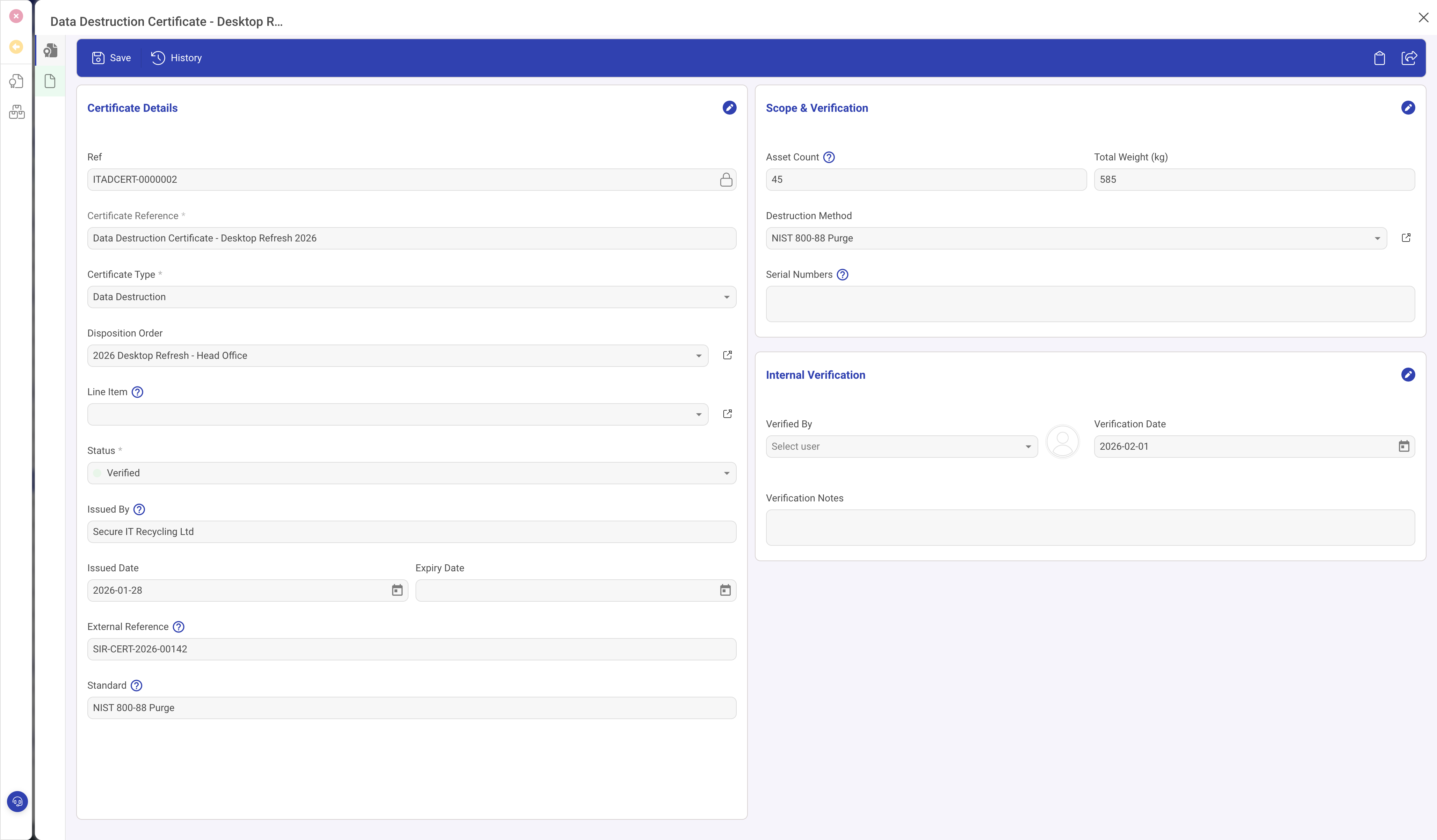
Certificate Details (left)
- Certificate Type, Disposition Order, Line Item (optional, for per-asset certificates).
- Status: Draft > Issued > Verified > Expired.
- Issued By: the ITAD vendor who issued the certificate.
- Issued Date, Expiry Date, External Reference (vendor's certificate number).
- Standard: the compliance standard referenced (e.g. "NIST 800-88 Purge", "R2", "e-Stewards").
Scope and Verification (right)
- Asset Count and Total Weight: what the certificate covers.
- Destruction Method: link to the destruction method lookup.
- Verified By and Verification Date: internal verification that the vendor-issued certificate is genuine and covers the correct assets.
- Verification Notes.
Scope: order-level vs line-level
A certificate can cover an entire disposition order (batch certificate) or a specific line item (per-asset certificate). Use order-level certificates for bulk processing where all assets were handled the same way. Use line-level certificates for high-value or high-security assets where individual accountability is required.
Destruction methods
The destruction methods lookup (ITAD > Destruction methods) defines the available processing methods. Each method has:
- Category: Data Destruction, Physical Destruction, Component Separation, or Chemical Processing.
- Compliance Standard: NIST 800-88, R2, e-Stewards, ADISA, BS EN 15713.
- Particle Size: maximum particle size for shredding methods (in mm).
- Suitable For: compatible media types (HDD, SSD, tape, paper, mixed).
- Certificate Required: flag that determines whether a certificate should be generated after processing.
Tips
- Always verify vendor-issued certificates against your asset list before marking them as Verified.
- Retain certificates indefinitely for audit and compliance purposes.
- Use the Certificate Required flag on destruction methods to ensure certificates are generated for every method that needs one.
- Upload the actual PDF certificate in the Documents panel for permanent record retention.